Posts
-
Let's Play Hell's Rebels! Adventure 01, Scene 02
This is the second scene in my solo Hell’s Rebels campaign. A long time passed between me completing the previous scene and writing up this one, but you’re seeing it published right after it since all the scenes were written long before their publication.
[GM] Long time no see!
I’m writing this post a full year after finishing the one for Scene 01! There are a lot of reasons for this large delay. For the first little while after I finished writing the Aria Park scene, I was just so dang satisfied with myself I didn’t feel the need to play more just yet. You don’t know how long I had that scene stuck in my head, and it was so nice to finally game it out.
After I started thinking about what to do next, I pretty soon ran into a major creative block stemming from a lack of battle maps. It kinda affected me when I was running stuff for other people over Roll20 too.
I can make lines on a blank canvas, but I’m not an artist, and stacking up my squiggles against the ready-made maps I also used made me very self-conscious. I finally broke through that by finding a tool that would let me draw decent-looking maps.
No, it’s not AI, and if you thought it was I’m disappointed in you. I just decided to spend some money on a copy of Dungeondraft once I found out it runs just fine on Linux. It has a huge library of textures and placeables that let me make pretty spiffy maps by hand. Sure, they’ll end up a bit standardized, but that’s still way better than my squiggles. It only uses square grids but I can export the images without a grid and let Foundry handle the hexes.
That gave me lots of ideas right away, but it was a relatively recent development. About two weeks ago as of this writing, I guess? I’ve been using some of my leisure time to implement those ideas, and to read Mythic Second Edition to see if I get any more.
Turns out I don’t quite need Mythic yet, there’s a cool thing I want to do. But let’s get the Mythic part over with anyway.
[GM] Mythic Bookkeeping
We can consider the whole Aria Park protest and riot to be our first scene. Chaos Factor started at 5, as standard, but there was pretty much no way it wasn’t going up to 6 here, no matter how the scene played out. So it’s 6 at the start of this scene.
Our current list of threads is:
- The Path
- Find Shensen (Rosalia, Arcturus)
- Contacting Ms. Docur (Jania)
- Find Rexus (Urist)
- Get Organized (Jade)
The Path is our “main story quest” as written in the books and modified by me when I’m wearing the GM hat. The others are each PC’s individual goals. Some can be solved in a fairly short time, others are more medium-or-long term unless we run into some amazing twists.
I’m going to add an asterisk to a thread whenever it’s advanced but not removed. The Path is going to get a lot of them, but it will be nice to remind ourselves of the progress we make in the others too.
Our list of characters is:
- The Dottari
- The Chelish Citizens Group
- The Red Jills
- The Asmodeans
There are a lot more people who might appear in the adventure but these are the groups who are in the original random encounter tables. They’ll do for now.
[GM] Scene 02: Fights in Tight Spaces
The original adventure transitioned PCs directly from the riot to another combat scene where they fought some CCG thugs and rescued Rexus. I’m going do something a little different. Let’s say I decided to alter the scene on my own, in Mythic terms.
Our group didn’t stick together as they escaped - they got out at different times and split up in the generalized chaos! The riot is dispersed but there’s still some confusion in the surrounding area. Bystanders who weren’t near the park find themselves having to flee alongside those who were, as opportunists roam around looking for people to rob and fascists roam around looking for people to arrest. Our heroes have to fight a bit more before they’re 100% clear.
I’ve prepared three different maps, all of them fairly “tight”, with a total size of 8 x 8 spaces and several obstructions that render them even more restricted. I’ll split our heroes into three distinct groups (2/2/1) and put them into each map alongside a randomly rolled encounter group that should contain between 1.5x-2x the number of “actions” available to them. At this stage the enemies are likely to be fairly weak but their numeric advantage will pose a challenge.
Whoever ends up alone will also find Rexus in the map.
Our Groups
My expectation would be that Jade and Rosalia are together because Jade followed Rosalia out. Jania and Arcturus are together by pure chance, and then Urist is alone and finds Rexus. That’s his goal, and he would have seen him from far away in the riot. Mythic, is that how things shake out1? I get an Exceptional Yes, which in this case isn’t any different from a normal Yes.
- Group 1: Jade & Rosalia.
- Group 2: Arcturus & Jania
- Group 3: Urist (and Rexus!)
Our Maps
Group 3 is getting the Alley map, because it makes sense that Rexus would be cornered there. Group 1 gets (roll roll) the Crossing map, and Group 3 the Tavern map.
Our Opposition
Urist is getting 5 CCG thugs as opposition. They’re pretty weak individually but so is Rexus and there’s a lot of them. That’s the same situation as in the book. I’m rolling to see which of the remaining entries on the Characters list faces each of the other groups.
(roll roll)
Group 2 is getting dottari. Three should do it.
Group 1 is getting Asmodeans. The entry for them in the Adventure One random encounter table has a group composed of a cultist (Cleric 3), and a Redactor (Monk 1). I’ll use a spellcaster inspired by the Iron Circle Dark Adept from Threats ot the Nentir Vale, and use a couple of Tar Devils from the same place instead of the monk. Can’t make it too easy for one of our best fighters.
[Player] Group 1: Jade & Rosalia, Crossing, vs. Asmodeans

An urban intersection where someone abandoned a cart full of produce in a hurry, causing some of its cargo to spill out. Our scene is set in an urban crossroad with an abandoned cart and a big box of produce taking up space in the center. Rosalia and Jade are also in the center, separated by the clutter and surrounded by enemies. A tar devil approaches from the north, another one from the south, and a hooded cultist from the west.
The PCs still have their weapons in hand, having just left the scene of the riot. The enemies are all ready too, since they were hunting “heretics” in this area.
Rosalia goes first and uses her Song of Humiliation to stun the Dark Adept, saving the day right there by preventing him from casting his Dartk Tendrils spell. Jade engages the Tar Devil closest to her and wounds his leg, though not quite enough to cripple it.
The adept soon recovers and begins fencing with Rosalia, and the other tar devil decides to go deal with the bigger threat and converges on Jade. The bard manages to poke the adept for a bit of damage, and he decides to step back and finally cast his big spell on her. Rosalia is grappled by shadow tendrils that erupt from the ground!
Fortunately, the adept’s careless movement puts him close to Jade, who has just finished dispatching the first tar devil and is within stepping distance of the adept’s back. She stabs him, and that’s that. Adept down, Rosalia released.
The two PCs have little trouble dispatching the remaining devil after that, with Rosalia stunning him and Jade finishing the job with a decapitating slash. Now stained by tarry ichor, the two continue their escape.
Analysis
The fight took 4 rounds overall and the “tight spaces” effect was keenly felt.
Player: The PCs were positioned such that an enemy facing one of them risked exposing their back to the other, which was pretty good! However, Rosalia could have made better use of her Song of Humiliation, instead of trying to stab the adept while Jade dealt with the tar devils alone. Still, stunning the dark adept for that first turn deactivated a major threat early on, as neither PC had great defenses against his Dark Tendrils spell.
GM: It was pretty hard dealing with the PC’s positioning. The Dark Adept should probably have kept trying to cast Dark Tendrils after he recovered from the initial stun. I was a bit too lenient here. The Tar Devils were also not a huge threat without their net attack from TNV, but I think this was okay because this is not supposed to be a deadly fight for the PCs. I’ll add that in the future.
[Player] Group 2: Arcturus & Jania, Tavern, vs. Dottari
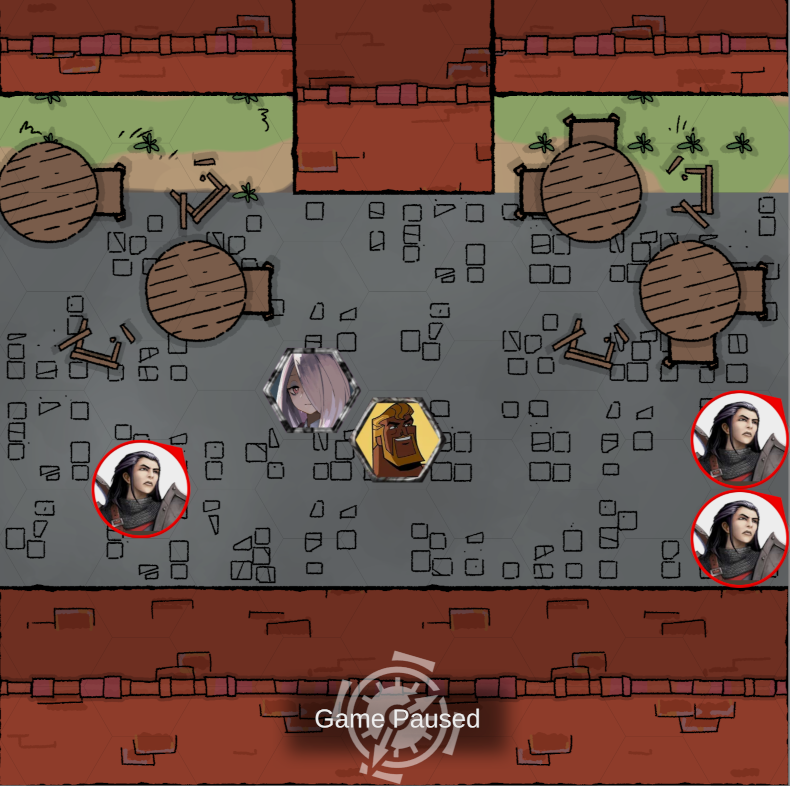
A tavern that was busy before the riot started a few streets over, causing the staff and patrons to run away. In the picture above we see a narrow street in front of a tavern, cluttered by tables and chairs. Jania and Art are in the center, back to back, with a dottario coming in from the west and two others from the east.
Arcturus does not have his knife in hand, but Jania has her cane. The dottari begin armed. This map is considerably more open than the Crossing, and this time it’s the dottari who have the advantage of positioning.
Arcturus starts the proceedings by performing a Heroic Charge on the single dottari to the left. He grabs him good. The other two close in on Jania, who tries but fails to feint one of them.
Arcturus is pretty deadly against a single opponent he can grab, but that leaves him vulnerable to other enemies. Fortunately he manages to slam the grappled dottari to the ground and deal enough damage to take him out, allowing him to turn to the others and get ready to defend himself. I played this as a Rapid Strike with another Wrestling grab to increase control points, and then spending all of those points on a single attack I resolved as a punch. That was 5d crushing!
Jania finds her cane does little to the guards through their armor, and Arcturus has some trouble grabbing the next one. He critically fails while defending against one of them, which lets him get bonked for 6 injury and makes him lose his balance until his next turn. Jania also gets bonked, and even a minimal damage roll takes half her HP away.
The tide turns on the next round, however, as Arcturus critically succeeds on a defense and causes the attacking guard to drop his mace! He then proceeds to grab him and carry him away from his buddy, finishing him off in the next couple of turns with a control-enhanced stab while Jania keeps the last guard busy.
Then Arcturus grabs the last guard and it’s time for Jania to have her revenge, as she steps behind the restrained dottario and uses her cane for a “backstab” (a Telegraphic and Determined All-Out-Attack to the skull with a Mighty Blows FP expenditure for extra damage). That causes a whopping 32 injury to the guard, more than enough to finish him off.
Analysis
This time the PCs had the positioning disadvantage. They took out the left flank of the pincer early, but the two remaining dottari were still effective at achieving superior positions here. Luckily for Arcturus, a character is only defenseless against attackers who start their turns on the character’s back hex. As it was, he had to defend against several “flanking” attacks from dottari, but luckily he managed them all. He also shows how luck is still a factor even for a PC that has combat skills as high as he does.
Altogether whis was a much more harrowing fight for our heroes even though dottari are less dangerous than tar devils.
[Player] Group 3: Urist & Rexus, Alley, vs. CCG Thugs
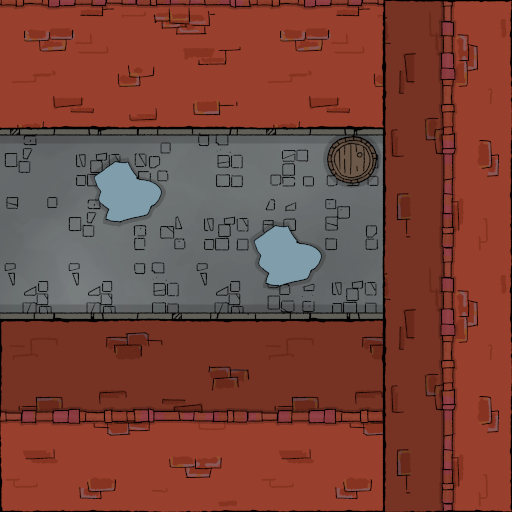
A dirty dead end alley at the end of a side street. I didn’t take a VTT screenshot for this one, so here’s the base map instead. We’re in a dead end alley at the end of a narrow street.
This one starts with Rexus cornered in the alley’s dead end, Urist at the mouth of the alley to the west, and 5 CCG thugs between them. I don’t have a character sheet for Rexus, as I don’t intend to make him a player character. He’s got a cane, Smallsword-14, damage 1d crushing, Parry 10F, Dodge 8, HP 10, and a couple hundred points in scholarly skills not useful for combat.
The thugs are still minions, and go down to any blow that deals at least 1 injury. Rexus can hold his own against them for a few turns if he focuses on defense, but Urist has no crowd control spells. He decides to spend a second casting Armor 3 on himself before charging into melee. This will save his life.
Two of the thugs keep focusing on Rexus, while the other three run to engage the new threat. Despite the enemy’s relative weakness, this turns out to be the longest fight of the three! The thugs roll terribly to hit with only skill-10, but they roll really well for their active defenses throughout most of the fight. So Urist has some real trouble hitting them with his axe swings or shield bashes.
At some point I switch to attacking with Rexus, but the again the minions suddenly turn into geniuses when it’s time to make a defense roll. Rexus’ defenses, on the other hand, are now unboosted, which means he gets hit a few times. Thankfully, the damage rolls are low and he loses only 4HP total.
Urist also fails some defense rolls, but his Armor spell means he only suffers a couple of points of injury even with the enemies rolling super well. Then he rolls a critical failure and drops his shield! Convinced he has enough armor to withstand the assault, the dwarf moves to making All-Out-Attacks (Double) with his axe, but even so it takes around three more turns until he finally manages to hit all the enemies surrounding him and finish the fight. By the time he does, Rexus has finished his side of it as well, aided by some timely critical failures on the part of the thugs.
Analysis
I had an inkling this would be a challenging fight but even so it ended up being a lot more eventful than I expected. It taught me that buffing spells matter, and that even minions can be a bother when they stick around long enough (thanks to a streak of good defense rolls). That left us with a 2.5:1 ration of enemy to PC actions for most of the fight. Individually Urist was quite a bit better than a thug, but if it wasn’t for the Armor spell he’d have been worn down by their numbers.
[GM] More Mythic Bokkeeping
Despite a few surprising rolls, the group did well in these fights, so Chaos Factor goes back down to 5.
We can consider Urist’s “Find Rexus” goal complete, of course. The original adventure gives XP for saving him, so the whole group gets 1 point. We can replace it with a “Reunite” thread - it’s not necessarily a goal of the characters, but it’s a goal of mine. Rescuing Rexus also advances The Path.
Our list of characters remains more or less the same. It’s just enemies for now, as anyone who could be an ally is laying low at the moment.
Chaos Factor: 5
Threads
- The Path *
- Find Shensen (Rosalia, Arcturus)
- Contacting Ms. Docur (Jania)
- Reunite!
- Get Organized (Jade)
Character
- The Dottari
- The Chelish Citizens Group
- The Red Jills
- The Asmodeans
- Rexus Victocora
-
Odds are 50/50 at Chaos 6, so actual chances are 13/65/94. I roll a 10. ↩
-
Hell's Rebels Bestiary: Nox and Mephiry
Part of the Bestiary for my solo Hell’s Rebels game.
Nox is technically the “final boss” for adventure 01, but she appears right in Scene 01 as a scary threat to run away from, and it’s conceivable Dungeon Fantasy Delvers might try to fight her here.
The Lore
The original adventure has more detail about her biography, but all we really need to know is that Nox is one of Barzilai Thrune’s loyal lieutenants, serving him voluntarily and gleefully. She can be found either acting as a bodyguard to him, or in command of a detachment of dottari or other minions on an “away mission”.
Barzilai has “rewarded” Nox by binding her soul to a bearded devil, giving her powerful regeneration and powers resembling the devil’s. In exchange, once she does die her soul will go straight to Hell.
The Numbers
Nox’s pet hell hound Mephiry is always close to her, so you get stats for both.
Nox
Nox is about as beefy as a starting Knight, with her infernal powers added on top. She’s obviously a boss monster, and follows all the usual rules as the PCs. She will employ all the fancy moves allowed by her high skill and Weapon Master advantage, will go for the most vulnerable targets, and will make the same HT rolls as a PC would when her hit points go into the negatives.
Her monster class is still Mundane despite the devil possession. Her regeneration can be neutralized by Holy attacks, overpowered by sufficiently extensive dismemberment (like a beheading), or bypassed by creative murder methods like suffocation or drowning.
If Nox realizes she’s going to lose the fight she will attempt to teleport away, which follows the normal rules for casting (and interrupting!) a spell, except that it requires no skill roll on her part.
ST 15; DX 14; IQ 10; HT 13;
Dodge 10; Parry 14 (glaive);
DR 0 (head); 7 (front body); 4/2 (everywhere else).
HP 15; Will 10; Per 10; FP 13;
Speed 6.25; Move 6; SM 0;
- Dwarven Dueling Glaive (20): 2d+7 cut or 1d+6 imp; Reach 1,2*.
- Emergency Infernal Teleport: Casting time 3 seconds, costs 5 FP; teleports her to a point about 150m from the starting position, and then she runs away on foot.
Relevant Traits: Combat Reflexes; High Pain Threshold; DR 15 (vs. fire); Regeneration 1 HP/second (but not against Holy attacks); Vulnerable to Holy attacks (1.5x damage); Weapon Master (dueling glaive);
Class: Mundane.
Equipment: Balanced dwarven glaive, Custom suit of armor (see below), mithral key, monetary loot (see below).
Mephiry the Hell Hound
Hell hounds are statted up in DF: Monsters, but here I’m making my own slightly beefier version based on that one, plus the Hound ally from DF5, plus my guidelines from this post.
I still haven’t decided if this will apply to every hell hound in the adventure or just to Mephiry. Treat her either as a Worthy or as a mini-Boss depending on how cruel you’re feeling towards your players, since she will likely fight alongside Nox. If on the other hand you’re feeling a bit more merciful, just use the hellhound stat block from DF: Monsters.
ST 13; DX 14; IQ 6; HT 14;
Dodge 11; DR 5 (15 vs. Fire); SM 0;
HP 13; Will 11; Per 11; FP 14;
Speed 7; Move 8/12;
- Bite (16): 1d+1 cutting plus linked 1d+1 control; 1d burning follow-up; Reach C.
- Claw (16): 1d+1 crushing; Reach C.
- Fire Breath (14): Costs 1 FP to use; 2d burning; Range 5/10, but treat as a melee attack similar to a jet spell.
Relevant Traits: Dependency (Mana); Immunity to Metabolic Hazards; Quadruped;
Class: Demon.
Loot!
Nox’s loot is elaborate enough that I think it needs a section on its own.
Her suit of armor has a Plate breastplate covering all of her “body” hit locations from the front, and light mail covering the limbs and the back of the body. It has no helmet, but the whole thing is enchanted with Fortify 1 and Lighten 1. As mentioned in the stat block, it gives DR 7 to the front of the body and DR 4/2 to all other locations. It’s worth $5425 and weights 13.95kg.
She has a belt pouch with 20 gold coins ($8000, 0.20kg) in it. In the original this was split up between miscellaneous coinage and diamond dust, but I think it’s worth simplifying.
After all this, the dwarven dueling glaive she wields is probably her cheapest possession ($400, 3kg).
-
Hell's Rebels Bestiary: Dottari Guard
Part of the Bestiary for my solo Hell’s Rebels game.
The Lore
The book uses “dottari” both as a singular and a plural, but I kinda want to use “dottario” for the singular both because it fits the pseudo-Italian theming of Cheliax, and because it sounds like “otário” (fool/asshole) in Portuguese.
The dottari are Kintargo’s city guard, responsible for keeping the peace and enforcing the law. From what I see in the books Thrune barely had to do anything to get them to fall in line and begin collaborating on his fascist takeover. There were no big purges, he just replaced their commander with someone who didn’t keep their worst impulses in check.
This tells me your typical dottario has a personality very similar to that of your typical CCG Thug. The only difference between them is that the dottario made the cut to get into the guard and receive its training.
The Numbers
A dottari guard as seen on Scene 01, with equipment matching their role as riot cops. As this is quite heavy, we include some variants afterwards.
They will try to surround and outnumber their opponents, focusing on what they perceive to the the greatest threats and attempting to isolate them from any allies.
Dottari met on patrol will whistle for backup if outnumbered, unless they happen to be doing something even their bosses would not approve of. The higher the area’s general security level, the faster reinforcements will be to arrive.
Dottari Guard
ST 12; DX 11; IQ 10; HT 12;
Dodge 7 (9); Parry 9U (11U) (mace); Block 9 (11);
DR 3/1 in torso, 1 elsewhere.
HP 12; Will 10; Per 10; FP 12;
Speed 6.00; Move 3; SM 0;
- Mace (13): 1d+4 cr; Reach 1.
- Shield Bash (12): 1d-1 cr; Reach 1.
Class: Mundane.
Equipment: Light Mail shirt, mace, medium shield (DB 2), whistle, manacles. Medium Encumbrance.
Variants
Dottari Beat Cop: Remove the shield, leaving the dottario at Light Encumbrance with Move 4, Dodge 8, and no Defense Bonus to Dodge or Parry.
Dottari Archer: Add a short bow and a quiver with 12 arrows, and the following attack:
- Short Bow (13): 1d-1 imp; Acc 1; Range 150/225.
Impressions
ADAB.
Dottari have middling offense when compared to a typical starting delver, but their defense is high enough to be annoying. That shield makes them succeed fairly often at their active defenses unless the PCs spend some effort to bypass it, or to otherwise inflict penalties on them. Feints, Deceptive Attacks, flanking, surprise, anything but facing a solid formation of them head-on.
Other good alternatives against them are stealth and mind-affecting magic, as their Per and Will are only average.
-
Hell's Rebels Bestiary: CCG Thug
Part of the Bestiary for my solo Hell’s Rebels game.
The Lore
CCG stands for “Chelish Citizen’s Group”. Basically, if we consider the government of Cheliax to be facist (and I do), these are your brownshirts. They were so happy with Barzilai’s ascension to power they formed an unofficial voluntary organization about it.
The CCG believes they have tacit permission from the big boss to hurt people just like they’ve always wanted to… and, in this, they’re right. Barzilai loves giving them privileged access to situations where they can help the dottari crush “seditious rebels”, or to hire them as contractors for tasks he can’t spare the manpower for. And when they spontaneously decide to do a cheeky bit of assault & battery or public torture, he turns a blind eye.
CCG thugs have the bare minimum of combat training and pretty much no tactical awareness unless directed by a more skilled leader. They’ll try to surround and repeatedly club the nearest victim until that victim stops moving. Their morale crumbles pretty fast once they see those victims are capable of fighting back.
The Numbers
CCG Thug
ST 10; DX 10; IQ 9; HT 10;
HP 10; Will 9; Per 9; FP 10;
SM 0; Speed 5.00; Move 4;
Dodge 8; Parry 9 (club); DR 1 (Torso);
- Club (10): 1d cr; Reach 1.
- Brawling Punch (10): 1d-3 cr; Reach C.
- Wrestling Grab (10): 1d-2 control (1d-4 one-handed); Reach C.
Traits: Your pick from Bully, Fanaticism (Thrune), Intolerance (Total) and other unpleasantness.
Class: Mundane.
Equipment: Padded vest, club, manacles, 2dx$5 in coins. Light Encumbrance.
Threat Level: Usually Fodder, but can go up to Worthy depending on the scenario.
Impressions and Design Notes.
A schlub with a club. They should pose very little threat to delvers, even as Worthies, unless they end up with a very long streak of good rolls. This happened a couple of times in my actual play, but that still led more to long fights than dangerous ones.
If you have a lot of CCG thugs in play and it feels like the fight is going to be a slog, feel free to have them break and run once a significant percentage of them (or one of their leaders) is taken down.
CCG thugs feature prominently in the first half of Adventure 01, but the PCs outgrow them after that and they get replaced by dottari guards as the rank-and-file human opposition.
-
Hell's Rebels Bestiary: Introduction
If you’ve been reading my recent posts here you know I’ve been playing a solo game of Hell’s Rebels using GURPS Dungeon Fantasy. And a big part of my preparation for actually playing that game involves converting monsters when necessary. So I thought, why not post them here? After all, monster-posting has come to be a big part of my brand here at Octopus Carnival.
Here’s how we’ll do it: I’ll post the converted enemies and NPCs here in the blog as they appear in our published session logs. I’ll add a project page for them where they will be ordered both in order of appearance, and in alphabetical order. You’ll get a brief description, GURPS stats, and my impressions on the monster, both from looking at the stats and actually facing the thing in play.
I’ll convert, and therefore post, only the monsters I actually use in play. Hell’s Rebels books usually have enormous random encounter tables and new monsters at at the end, but I gather most people ignore the former and the later never appear on the adventure itself. I’ll leave those alone unless I actually have a use for them in my game. And of course, if I cook up a new monster for use in the game, it will also show up here.
subscribe via RSS